11 November 2023
How to configure a firewall in CentOS7

Introduction
FirewallD is a firewall management solution, which is available for many Linux distributions. It works as a frontend for the iptables packet filtering system encompassed by the Linux kernel.
FirewallD Daemon manages a group with a lot of rules to use an entity named "Zones". The rules that define the zones, depending on the level of your faith in your computer networks, no traffic should be permitted. The network interfaces are identified in a zone to indicate that firewalls should be allowed.
Such a computer can be a frequent network (such as a laptop), due to such flexibility, it is a good way to change your rules depending on your environment. While working on the public Wi-Fi network, there may be strict rules for banning most of your traffic while approving more robust constraints while connecting to your home network.
Install and Enable Your Firewall
Firewall is installed by default in some Linux distributions. You need to enable firewalls for your needs.
To install firewalld, use the following command.
sudo yum install firewalld
After installing firewalld you will have to enable the firewall and reboot the server.
To enable firewalld, use the following command.
sudo systemctl enable firewalld
sudo reboot
When the server restarts, your firewall should be reached, your network interfaces should be included in the configured zones you are configured to (or return to the configured default zone).
Now you can check that your service is working properly. To do this, use the following command.
sudo firewall-cmd --state
This command indicates that your firewall is working correctly and with the default configuration.
The default configuration of the firewall is always in the public zone.
To check the default configuration of the firewall, follow the command below.
firewall-cmd --get-default-zone
Since we did not issue any deviation from the firewalld default zone, and no interface is configured to connect to another region, that area is simply "active" zone (the area that controls the traffic for our interface). To verify it, use the following command:
firewall-cmd --get-active-zones
Here, we can see that our server has a network interface that is being controlled by the firewall (venet0). It is currently being operated according to the prescribed rules for the public zone. How do you know the rules related to public zones? You can print the configuration of the default zone by typing:
sudo firewall-cmd --list-all
From the output we can say that this area is the default and active “venet0” interface associated with this zone.
Follow the following command to find information about any other region outside of the default region.
firewall-cmd --get-zones
You can see the specific configuration with a zone by including the --zone= parameter in your --list-all command.
sudo firewall-cmd --zone=home --list-all
You can out all Zones definitions using the “--list-all-zones” option.
sudo firewall-cmd --list-all-zones | less
Select a Zones for your interface
If your network interface is not configured then every interface will be put in the default zone when the firewall is booted.
If you want, you can change the zone of an interface. Here we change "venet0" from the public zone to the home zone.
sudo firewall-cmd --zone=home --change-interface=venet0
If you want to check the changes zones of your interface, then you can see the active zones.
firewall-cmd --get-active-zones
If you want to select a default zone, then follow the following command.
sudo firewall-cmd --set-default-zone=home
The firewalld service lets you configure controllable rules and rules controls that take into account the environment of your network. It allows the transition of various firewall policies through the use of the zone and gives administrators the ability to adjust port management to more friendly service definitions.
Related Blog Post
Create, collaborate, and turn your ideas into incredible products with the definitive platform for digital design.
12 December 2022
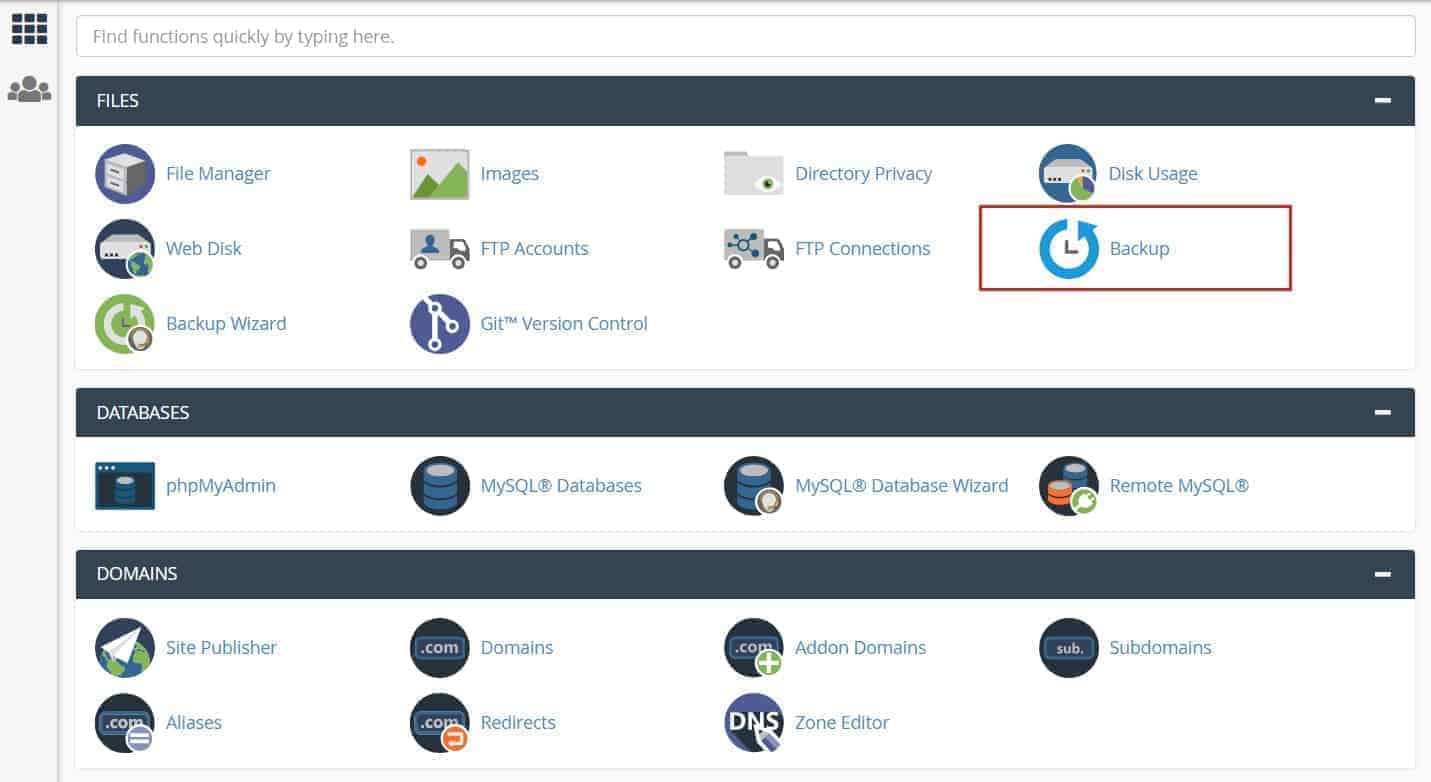
How to create cPanel backup from command line
This article explains how you can create cPanel backup from the command line, using your own username and password.
12 December 2022
How to install Webuzo Panel on linux Server
Webuzo is a popular alternative to cPanel, a widely used web hosting control panel developed by cPanel, Inc.
02 February 2022
What are NFT Domains?
NFT domains are new web extensions that are deployed using ERC 721 and Polygon Network, except .zil which uses Zilliqa.
01 January 2022
How to Delete a MySQL® Database
This document describes how to manually delete a MySQL® database from a cPanel & WHM server. This is useful if, for exa

11 November 2021
How to get Transfer Authorization Code from GoDaddy
To transfer your domain with us then must need EPP Code.